SCIM (System for Cross-domain Identity Management) lets your identity provider (IdP) automatically manage Base44 workspace members. When someone joins or leaves your organization in your IdP, Base44 is updated automatically, with no manual invites or removals needed.Documentation Index
Fetch the complete documentation index at: https://docs.base44.com/llms.txt
Use this file to discover all available pages before exploring further.
SCIM provisioning is available on enterprise workspaces only. Contact your account manager to enable it.
Workspace version
Base44 recently released an updated workspace version. The version your workspace is on affects how you configure SCIM, so it is important to know which one you have before getting started.| V1 workspaces | V2 workspaces | |
|---|---|---|
| Member attribute | seatType | role and creditLimit |
| Access model | Per-seat plans | Shared credit pool with role-based access |
| Capacity check on add | Yes, fails if no seats are available | No, members are added without a capacity limit |
Before you begin
Before setting up SCIM, make sure you have:- An enterprise workspace with SCIM enabled
- Admin access to your Base44 workspace
- Your workspace ID (the string after
/workspace/in your Base44 workspace URL) - A Base44 API key (found in Settings → API keys in your workspace)
Setting up SCIM with Okta
Okta is the recommended identity provider for SCIM provisioning with Base44.Auth0 does not support SCIM on the free tier. Use Okta if you need to test SCIM provisioning.
Step 1: Create a SCIM app in Okta
Okta OIDC apps do not support SCIM directly, so you need a separate SCIM app. To create a SCIM app:- In Okta, go to Applications → Browse App Catalog.
- Search for SCIM 2.0 Test App (Header Auth).
- Click Add Integration.
- Name the app (for example,
Base44 - SCIM Provisioning). - Click Done.
Step 2: Connect the app to Base44
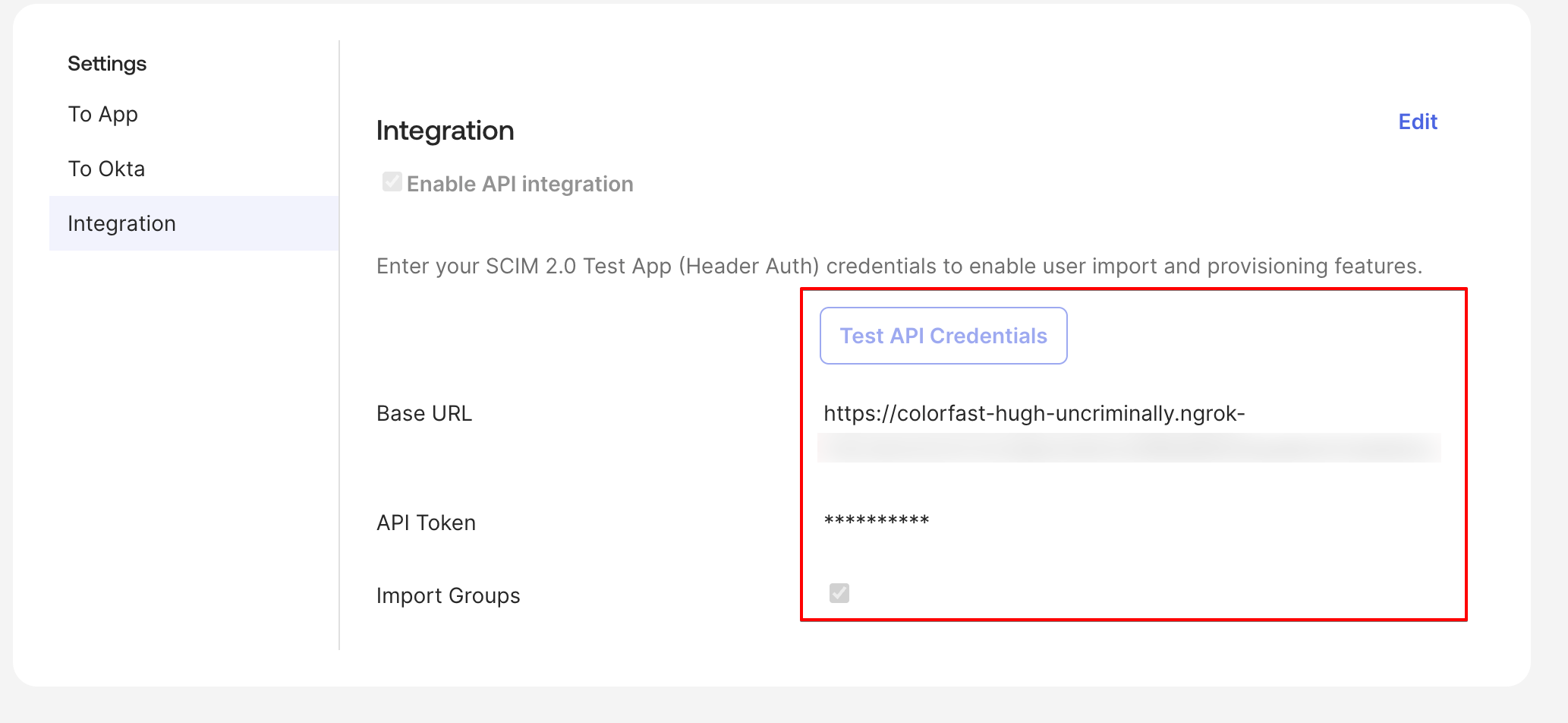
Point Okta to your Base44 workspace by entering your SCIM base URL and API key. To configure the API integration:- Open your new SCIM app and go to the Provisioning tab.
- Click Configure API Integration.
- Check Enable API integration.
- Set the SCIM 2.0 Base URL to:
Replace
{your-workspace-id}with your actual workspace ID. - Set API Token to your Base44 API key (without a “Bearer” prefix).
- Click Test API Credentials. You should see a success confirmation.
- Click Save.
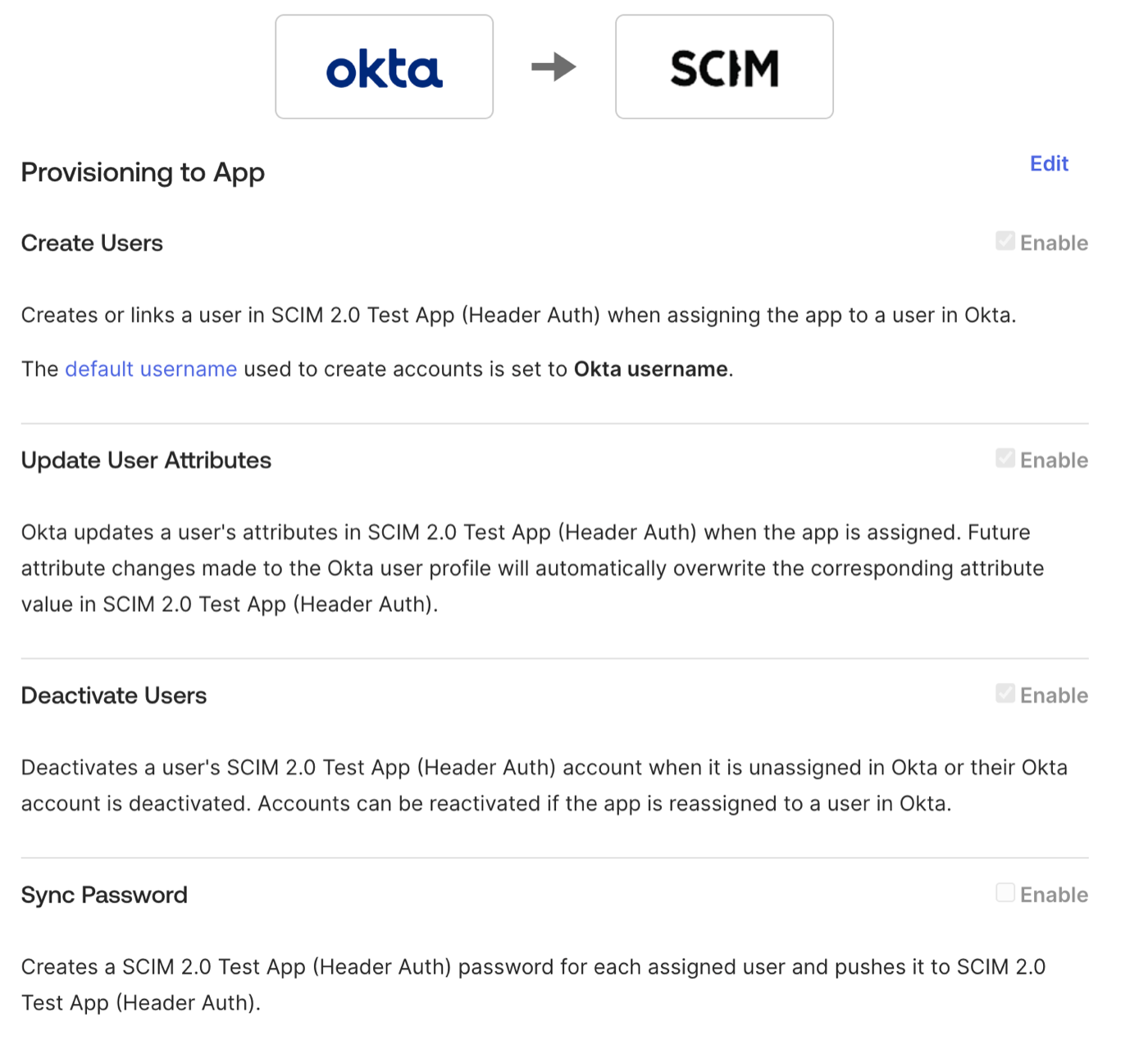
Step 3: Enable provisioning actions
Choose which actions Okta can perform on Base44 workspace members. To enable provisioning:- In the Provisioning tab, click To App.
- Enable:
- Create Users
- Update User Attributes
- Deactivate Users
- Click Save.
Step 4: Set up custom attributes
The custom attributes you create depend on your workspace version.V2 workspaces: role and credit limit
To add therole attribute:
- Go to Directory → Profile Editor and find your SCIM app.
- Click Add Attribute.
- Fill in the settings:
- Data type: String
- Display name: Role
- Variable name:
role - External name:
role - External namespace:
urn:base44:params:scim:schemas:extension:user:2.0 - Enum: Check Define enumerated list of values and add
admin,editor,viewer - Attribute required: No
- Click Save.
creditLimit attribute (optional):
Skip this if you do not want per-member credit caps. The default is no cap.
- In the same Profile Editor, click Add Attribute.
- Fill in the settings:
- Data type: Integer
- Display name: Credit Limit
- Variable name:
creditLimit - External name:
creditLimit - External namespace:
urn:base44:params:scim:schemas:extension:user:2.0 - Attribute required: No
- Click Save.
- Go to your SCIM app → Provisioning → To App → Attribute Mappings.
- Set:
userName←user.emailrole←"editor"(or map from your IdP’s role attribute)creditLimit← your preferred value or IdP attribute (if you added it)
- Remove any unsupported mappings (firstName, lastName, displayName,
seatType). - Click Save.
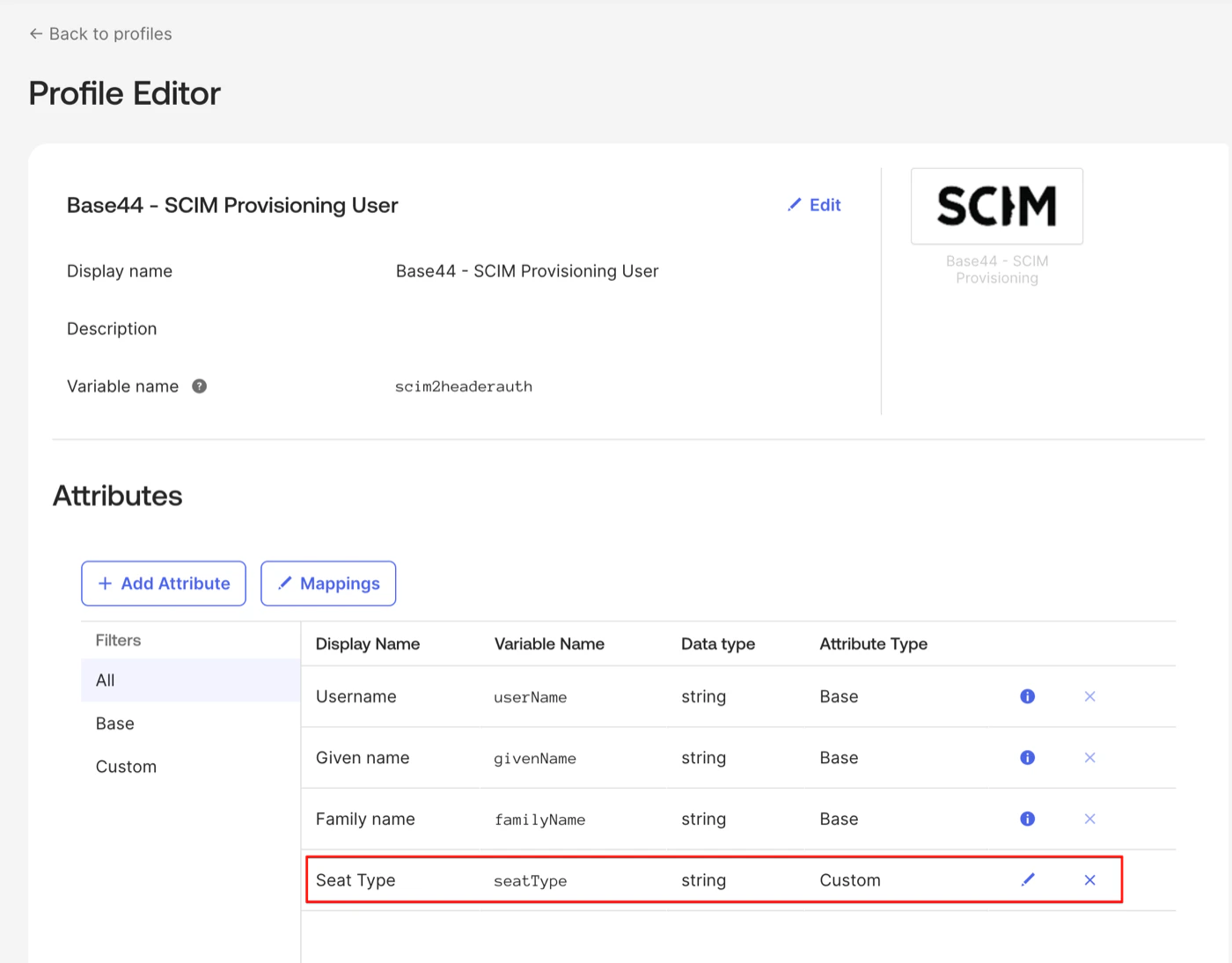
V1 workspaces: seat type
To add theseatType attribute:
- Go to Directory → Profile Editor and find your SCIM app.
- Click Add Attribute.
- Fill in the settings:
- Data type: String
- Display name: Seat Type
- Variable name:
seatType - External name:
seatType - Enum: Check Define enumerated list of values and add
starter,builder,pro,elite,elite_2,elite_3 - Attribute required: No
- Click Save.
- Go to your SCIM app → Provisioning → To App → Attribute Mappings.
- Set:
userName←user.emailseatType←"builder"(or map from your IdP’s attribute)
- Remove any unsupported mappings (firstName, lastName, displayName,
role,creditLimit). - Click Save.
Step 5: Test provisioning
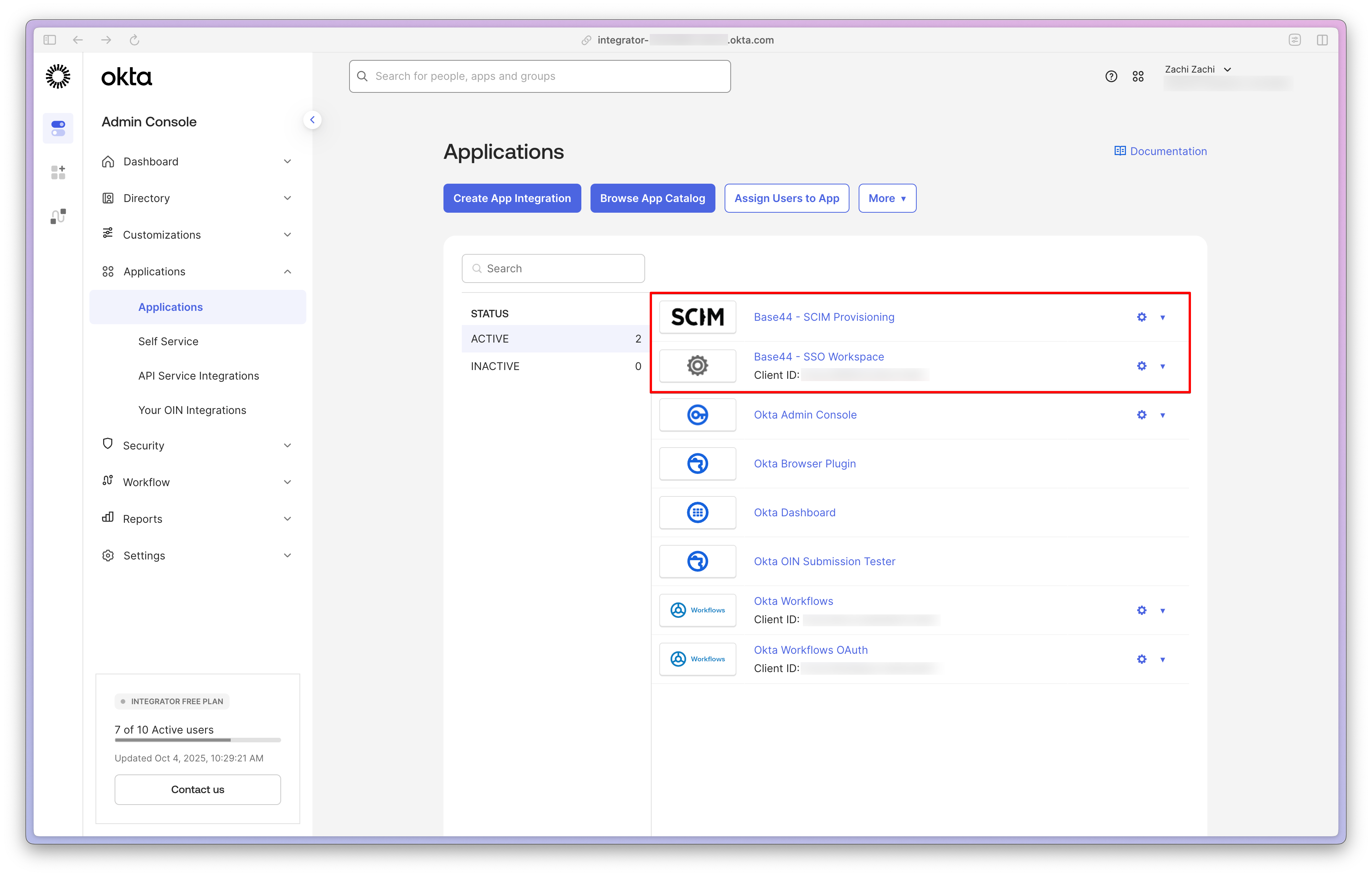
Assign a test user to confirm that provisioning and deactivation work as expected.Each user must be assigned to both your Base44 SSO app and your Base44 SCIM Provisioning app in Okta. Assigning to SCIM only will provision the user but they will not be able to log in via SSO.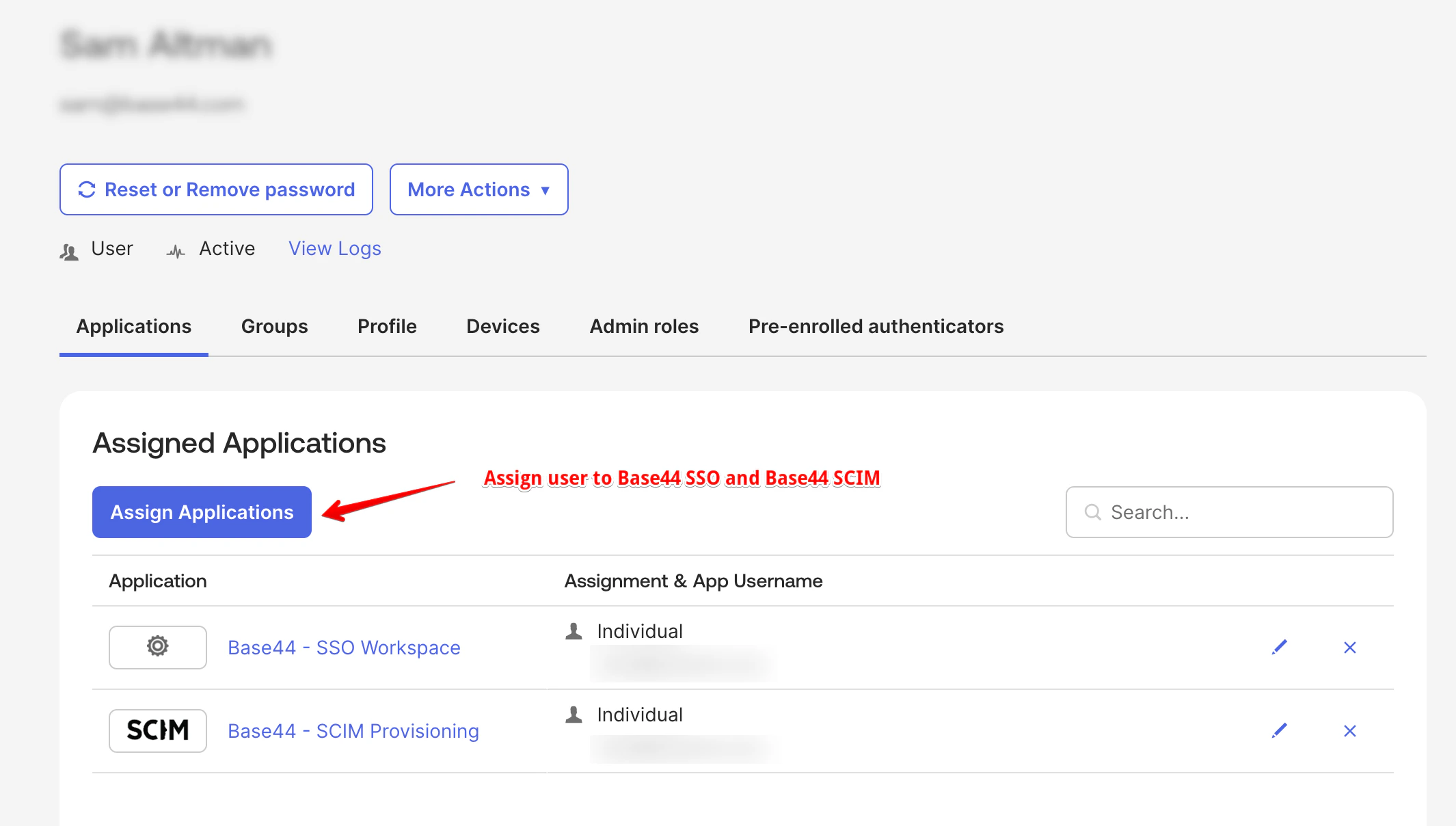
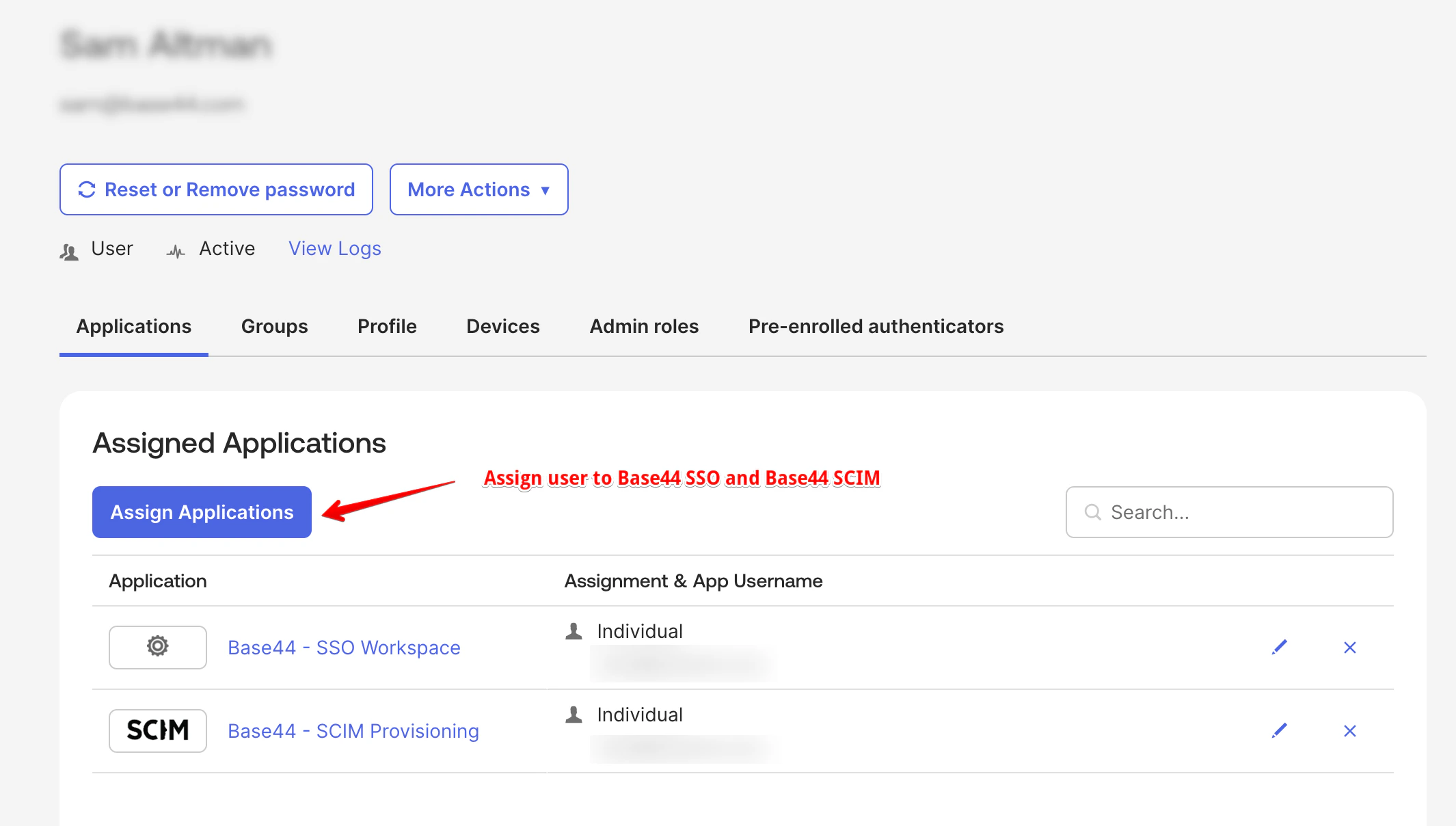
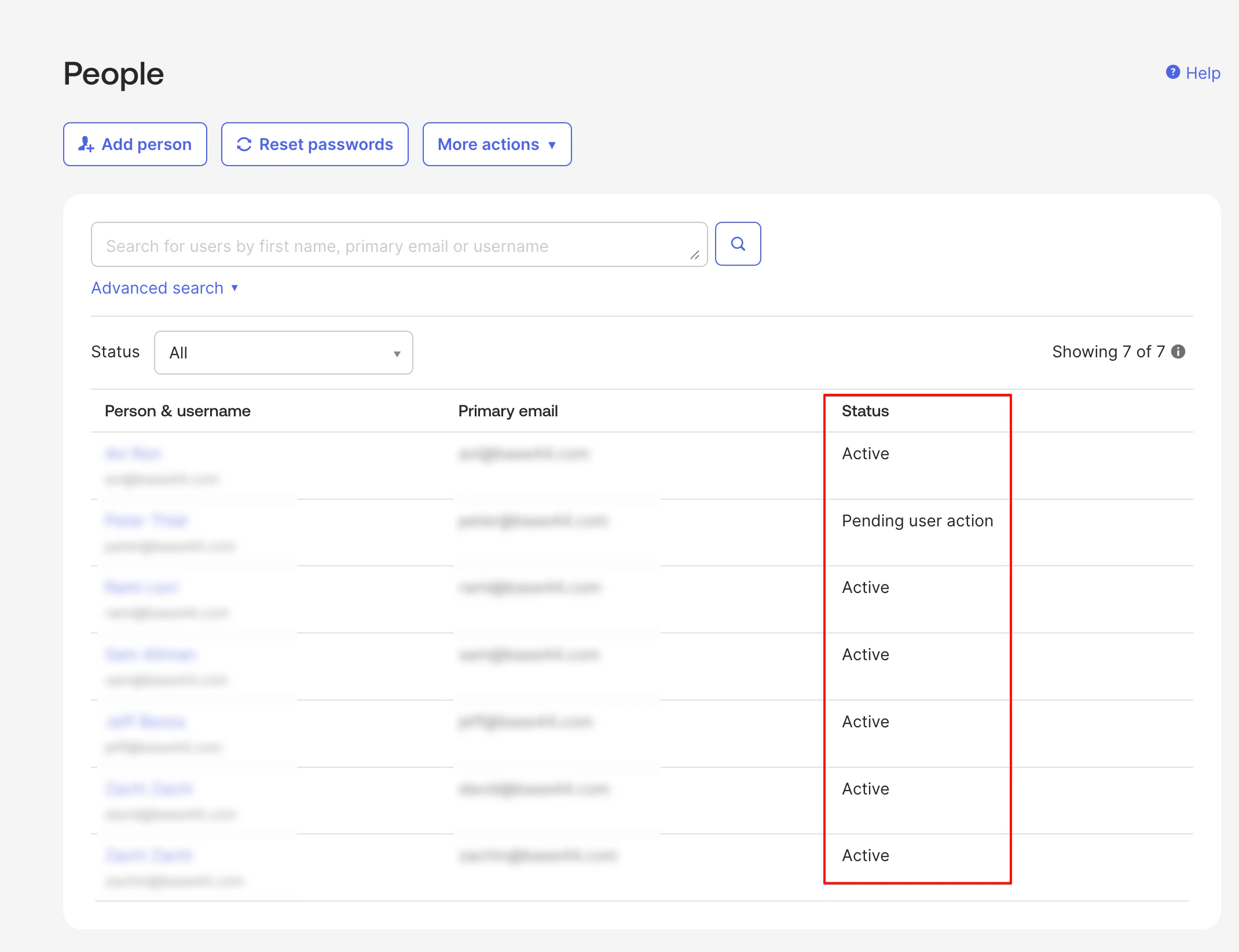
- In Okta, go to Directory → People.
- Click on your test user.
- Go to the Applications tab.
- Click Assign Applications.
- Select Base44 - SSO Workspace and Base44 - SCIM Provisioning, then click Assign.
- Set the required attribute:
- V2: Set
roletoeditor,admin, orviewer. Optionally setcreditLimit. - V1: Set
seatTypeto a valid value (for example,builder).
- V2: Set
- Click Save and Go Back → Done.
- Check your Base44 workspace members to confirm the user appeared.
- In the Assignments tab, click Unassign next to the test user.
- Confirm the removal.
- Check that the user no longer appears as an active member in Base44.
Managing your members
Once SCIM is set up, Okta handles membership changes automatically. Here is what happens in Base44 for each action.Adding members
When you assign a user to your SCIM app in Okta, Base44 creates their workspace membership automatically. The user can sign in to Base44 using SSO once they are provisioned.Updating members
When you update a user’s attributes in Okta (such as their role or credit limit), Base44 updates their workspace membership to match.Workspace owners cannot be updated or deactivated via SCIM. Owners must be promoted or demoted from the Base44 dashboard directly.
Removing members
When you unassign a user from your SCIM app, Base44 removes them from the workspace. Their platform-wide Base44 account is not deleted, and they retain access to any other workspaces they belong to. If you need to re-add a previously removed member, re-assign them in Okta. Base44 will create a new workspace membership.Roles (V2 workspaces)
V2 workspaces use roles instead of seat types to control what each member can do. You assign a role when provisioning a user via SCIM, and you can update it at any time.| Role | What they can do |
|---|---|
admin | Manage members, billing, and workspace settings |
editor | Build, edit, and run apps; uses credits from the workspace pool |
viewer | Read-only access to apps; does not consume credits |
owner, member, and guest roles cannot be assigned via SCIM. If your IdP has groups mapped to those roles, update the mapping to use admin, editor, or viewer instead.Per-member credit limits
On V2 workspaces, you can optionally cap how many credits a single member can use per month. SetcreditLimit to a positive integer to apply a cap, or leave it empty for no limit.
Credit limits only apply to admin and editor roles. Viewers cannot consume credits, so setting a credit limit on a viewer returns an error.
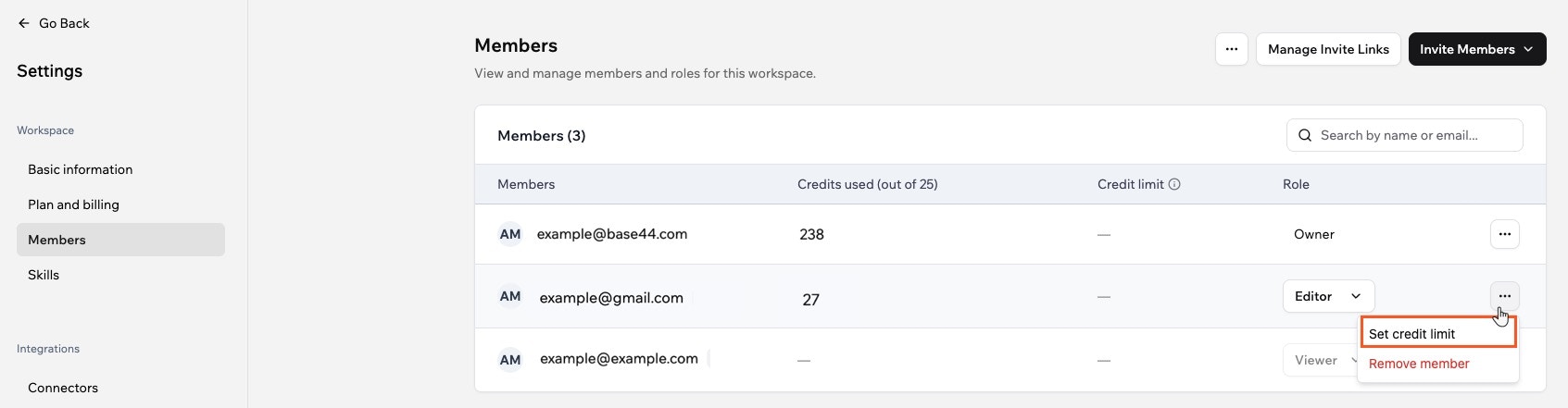
You can also set credit limits directly from your workspace settings without going through SCIM.
To set a credit limit for a member:
- Click your profile icon in your workspace.
- Click Settings.
- Click Members.
- Click the More Actions icon ••• next to the relevant member.
- Click Set credit limit, enter the limit, and click Save.
Troubleshooting
If provisioning is not working as expected, the steps below cover the most common errors and how to fix them.API credentials test failed in Okta
API credentials test failed in Okta
Check that your API key is correct and does not include a “Bearer” prefix. Verify the SCIM base URL contains the correct workspace ID. If you are testing locally, confirm ngrok is running and the URL is up to date.
User is not being provisioned
User is not being provisioned
Check the Okta provisioning logs for specific errors. For V2 workspaces, confirm
role is set to admin, editor, or viewer. For V1 workspaces, confirm seatType is a valid value and that your workspace has available seats of that type."seatType is not supported on V2 workspaces" error
"seatType is not supported on V2 workspaces" error
Your Okta profile is sending
seatType to a V2 workspace. Remove the seatType attribute from the Profile Editor for your SCIM app and add role instead. Even sending seatType with an empty value causes this error."role is not supported on V1 workspaces" error
"role is not supported on V1 workspaces" error
Your Okta profile is sending
role to a V1 workspace. Remove the role and creditLimit attributes from the Profile Editor and add seatType instead.Workspace owner cannot be updated or deactivated
Workspace owner cannot be updated or deactivated
This is by design. Workspace owners must be promoted or demoted from the Base44 dashboard. SCIM cannot modify owner memberships.
Cannot set a credit limit for viewers error
Cannot set a credit limit for viewers error
creditLimit can only be set on admin or editor roles. Either change the role to editor or admin, or remove the creditLimit value.